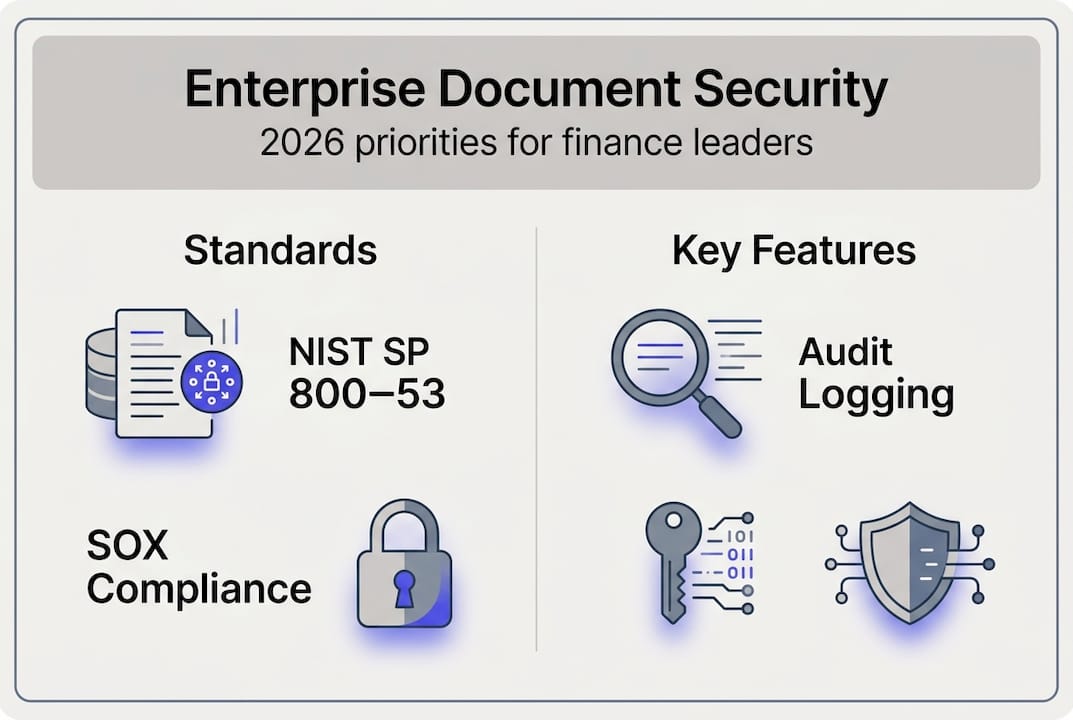
Enterprise document security guide for finance leaders 2026

Most finance leaders assume that slapping AES-256 encryption on a document management system (DMS) is enough to satisfy auditors and regulators. It is not. The real threat landscape for financial documents spans misconfigured access controls, AI-driven data leakage, and a patchwork of overlapping regulations that each demand something slightly different. NIST SP 800-53 controls like Access Control, Configuration Management, and System and Information Integrity form the backbone of enterprise-grade document security, yet most organizations only implement a fraction of them. This guide walks you through the full picture: regulatory requirements, technical controls, AI risks, and the KPIs that tell you whether your security posture is actually working.
Table of Contents
- Why security is non-negotiable for financial document management
- Key enterprise security standards: NIST SP 800-53 explained
- Critical security features for compliant document management systems
- AI, automation, and the latest security challenges
- Best practices and KPIs for ongoing secure document operations
- Empower your enterprise with secure, compliant document management
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Regulations drive security | Financial firms must align document management with SOX, HIPAA, and GDPR requirements to avoid fines and breaches. |
| NIST controls are foundational | Implementing NIST SP 800-53 standards provides strong access, configuration, and integrity controls for enterprise security. |
| Modern DMS features | Look for encryption, granular access, audit logs, and automated retention to meet compliance and operational needs. |
| AI adds risk and opportunity | AI tools boost efficiency but require strict controls to prevent unintended exposure of sensitive information. |
| Continuous improvement required | Secure document management is an ongoing process that demands regular review, monitoring, and automation. |
Why security is non-negotiable for financial document management
Financial institutions are among the most targeted organizations in the world. Attackers know that a single breach of a bank statement archive or audit file can yield account numbers, tax IDs, and transaction histories in bulk. Beyond the immediate financial loss, the regulatory fallout can be devastating.
Understanding document security in finance means recognizing that compliance is not a checkbox. SOX, HIPAA, and GDPR requirements each impose distinct obligations: SOX Section 802 mandates tamper-proof storage for audit records, HIPAA requires encryption and access logs for electronic protected health information, and GDPR enforces data minimization and geographic residency rules. Violating any one of them can trigger fines that dwarf the cost of proper security infrastructure.
Here is what poor document security actually costs you:
- Regulatory fines: GDPR penalties reach up to 4% of global annual revenue
- Litigation exposure: Tampered or missing audit records can void legal defenses
- Reputational damage: A single publicized breach erodes client trust for years
- Operational disruption: Incident response and remediation consume enormous internal resources
“Compliance benchmarks are not optional guardrails. SOX Section 802 mandates tamper-proof storage, HIPAA requires ePHI encryption and access logs, and GDPR emphasizes data minimization and residency.” Basic encryption addresses only one layer of a multi-layer problem.
The takeaway is simple: standard security tools protect data at rest, but financial document management demands controls that govern who touches data, when, how, and with what authority.
Key enterprise security standards: NIST SP 800-53 explained
NIST SP 800-53 is the federal catalog of security and privacy controls used by government agencies and increasingly adopted by private-sector enterprises as the gold standard for information security. For financial document management, three control families matter most.
Access Control (AC) governs who can read, edit, or delete documents. In a DMS context, this means role-based access control (RBAC), least-privilege policies, and session timeouts. Configuration Management (CM) ensures your system settings do not drift into insecure states over time. Think automated baseline checks and change-approval workflows. System and Information Integrity (SI) covers malware protection, security alerts, and integrity verification of stored files.
| NIST Control | What it means | DMS feature it maps to |
|---|---|---|
| AC-2 Account Management | Manage user accounts and permissions | RBAC, provisioning workflows |
| AC-17 Remote Access | Secure remote connections | MFA, VPN enforcement |
| CM-6 Configuration Settings | Enforce secure baseline configs | Automated compliance scans |
| SI-3 Malware Protection | Detect and block malicious code | File scanning on upload |
| SI-7 Software Integrity | Verify files have not been altered | Cryptographic hash verification |
To evaluate your current system against these controls, follow this sequence:
- Map every document type to a sensitivity tier (public, internal, confidential, restricted)
- Audit existing user roles and remove any accounts with broader access than their job requires
- Run a configuration baseline scan and document deviations
- Verify that file integrity checks are active and logged
- Test your incident response plan against a simulated unauthorized access event
Pro Tip: When evaluating cloud-based DMS platforms or AI integrations, ask vendors to provide their NIST SP 800-53 control mapping documentation. If they cannot produce it, that is a red flag worth taking seriously. Review security best practices for SMEs to see how these controls scale across organization sizes.
Critical security features for compliant document management systems
Frameworks tell you what to achieve. Features tell you how. Any DMS handling sensitive financial data must include a specific set of technical and operational capabilities to meet regulatory requirements.
Key security features for financial services include AES-256 encryption at rest and in transit, multi-factor authentication (MFA), granular RBAC permissions, full audit logging of every action, and WORM (Write Once, Read Many) compliance for non-rewritable records under SOX, SEC, and FINRA rules.

| Feature | Why it matters | Compliance mandate |
|---|---|---|
| AES-256 encryption | Protects data if storage media is compromised | HIPAA, GDPR, SOX |
| Multi-factor authentication | Blocks credential-based attacks | NIST AC-17, FINRA |
| Granular RBAC | Limits blast radius of insider threats | SOX, SEC Rule 17a-4 |
| Immutable audit logs | Proves chain of custody for regulators | SOX Section 802 |
| WORM storage | Prevents record alteration or deletion | SEC, FINRA, SOX |
| Automated retention | Enforces 7-year SOX retention without manual effort | SOX Section 802 |
Beyond the table, a few operational features separate adequate systems from genuinely secure ones:
- Automated retention scheduling removes the human error factor from document lifecycle management
- Watermarking and download tracking create accountability for every exported file
- Geo-restricted storage satisfies GDPR data residency requirements without manual intervention
Pro Tip: Avoid blanket access grants for auditors or external partners. Create time-limited, read-only permission sets scoped to specific document folders. This protects you during audits without exposing your entire archive. Explore secure workflows for financial data to see how permission layering works in practice.
AI, automation, and the latest security challenges
AI-powered document processing is transforming how finance teams handle bank statements, invoices, and audit files. Speed and accuracy gains are real. So are the new attack surfaces.
Large language models (LLMs) and intelligent document processing (IDP) tools extract structured data from unstructured documents at scale. But when those models index financial documents, they can inadvertently embed personally identifiable information (PII) into vector databases, making that data retrievable by anyone with query access. Secure LLM indexing practices require redaction of PII and financial data before embedding generation, k-anonymity in retrieval pipelines, and local or confidential compute environments to prevent leakage.
The adoption numbers make this urgent. 78% IDP adoption across financial services is already high, but security remains the top implementation hurdle. That gap between adoption and security maturity is where breaches happen.
Here are the defensive controls every finance team should implement before deploying AI document tools:
- Redact PII and account numbers from documents before they enter any AI pipeline
- Restrict model query access using the same RBAC policies applied to your DMS
- Use retrieval-augmented generation (RAG) architectures that ground AI responses in approved document sets only
- Log every AI query and output for audit trail continuity
- Run periodic red-team exercises to test whether sensitive data is retrievable through model queries
The organizations getting this right are treating AI as an extension of their document management perimeter, not a separate tool. Automated processing for document security and [AI document processing insights](https://bankstatementflow.com/blog/ai document processing revolution) both show how automation, when properly governed, reduces risk rather than amplifying it.
Best practices and KPIs for ongoing secure document operations
Security is not a one-time implementation. It is a continuous operational discipline. The organizations that maintain compliance over time are the ones that monitor, measure, and improve systematically.
Start with a continuous monitoring cycle built around three steps: scan, classify, and remediate. Data scanning tools identify ROT (redundant, obsolete, trivial) data and unclassified sensitive files across your document repositories. AI classification then tags documents by sensitivity and applies the correct retention and access policies. Remediation closes the gaps: deleting ROT data, reclassifying mislabeled files, and revoking stale permissions.
Track these KPIs to measure your security posture over time:
- PII detection recall: What percentage of documents containing PII are correctly identified by your scanning tools?
- Audit log latency: How quickly are access events recorded and available for review?
- Policy violation rate: How many unauthorized access attempts or permission overrides occur per month?
- Retention compliance rate: What percentage of documents are on the correct retention schedule?
- Mean time to remediate: How long does it take to close a detected security gap?
Beyond metrics, layer human review into your automation workflows. Automated tools catch the majority of issues, but edge cases, unusual access patterns, and novel attack vectors still require human judgment. Schedule quarterly security reviews that combine automated scan reports with manual spot-checks of high-sensitivity document folders.
[AI accuracy in finance](https://bankstatementflow.com/blog/ai improve accuracy finance) and [AI for bank statement accuracy](https://bankstatementflow.com/blog/why use ai for bank statements accuracy 2026) both demonstrate that the highest-performing finance teams treat accuracy and security as inseparable disciplines, not competing priorities.
Pro Tip: Automate ROT cleanup on a monthly schedule. Redundant and obsolete documents sitting in your archive are not just storage waste. They are unmonitored exposure points that expand your attack surface without adding any business value.
Empower your enterprise with secure, compliant document management
Every framework, feature, and KPI covered in this guide points toward the same conclusion: financial document security requires a platform built for it from the ground up, not a general-purpose tool with security bolted on afterward.
BankStatementFlow is a secure AI-powered bank statement converter designed specifically for financial teams that cannot afford security gaps. The platform applies enterprise-grade encryption, granular RBAC, and full audit logging to every document it processes, whether that is a password-protected PDF, a scanned image, or a multi-page bank statement in a regional format. You get up to 99% extraction accuracy without sacrificing the compliance controls your auditors and regulators require. The online statement conversion tool integrates directly into existing workflows via API, so your internal controls extend to every document that moves through the system. No security gaps, no manual workarounds.
Frequently asked questions
What is the most important security feature for financial document management?
Tamper-proof storage, specifically WORM compliance and audit logging, is the foundation of legal defensibility. Without it, you cannot prove that records have not been altered after the fact.
How do AI and automation impact document security?
AI accelerates processing but introduces risks like PII embedding in model indexes. Secure LLM indexing requires redaction before data enters any AI pipeline, plus strict access controls on model queries.
What retention schedules are required for financial statements?
SOX mandates seven years of retention for audit-related financial documents. Automated enforcement is strongly recommended to eliminate manual errors and ensure consistent compliance.
What KPIs should I track to ensure ongoing security?
Focus on PII detection recall and audit latency as your primary indicators, then layer in policy violation rates and mean time to remediate for a complete picture of your security maturity.
Recommended
- Document security in finance for SMEs in 2026 - BankStatementFlow Blog
- What is financial document automation? A 2026 guide - BankStatementFlow Blog
- Optimize secure financial data workflows with automation - BankStatementFlow Blog
- Master financial document organization: 99% accuracy guide - BankStatementFlow Blog