Document security in finance for SMEs in 2026

Many small and medium-sized enterprises believe that basic firewalls and antivirus software adequately protect their financial documents. This misconception puts them at serious risk. Data breaches in financial services cost organizations an average of $5.9 million in 2026, representing a 15% increase over three years. A tailored document security framework is no longer optional for SMEs handling sensitive financial information and striving to maintain regulatory compliance.
Table of Contents
- Understanding Document Security Frameworks In Finance
- Technologies And Architectures Securing Financial Documents In 2026
- Navigating Regulatory Compliance And Risk Management With Document Security
- Implementing Document Security Best Practices In SME Finance Operations
- Explore AI-Powered Document Security Solutions
Key takeaways
| Point | Details | |-------|---------|| | Lifecycle protection | Document security frameworks safeguard critical financial data across its entire lifecycle, ensuring only authorized users handle sensitive information. | | Cost reduction | Strong document security reduces costly breaches and ensures regulatory compliance with standards like PCI-DSS and GDPR. | | Technology integration | Emerging technologies like zero trust architecture and AI-powered threat detection enhance security but require careful implementation. | | Multilayered approach | SMEs benefit from standards-based cybersecurity frameworks that provide cost-effective, comprehensive protection. | | Actionable implementation | Practical steps exist to implement effective document security in financial operations without overwhelming resources. |
Understanding document security frameworks in finance
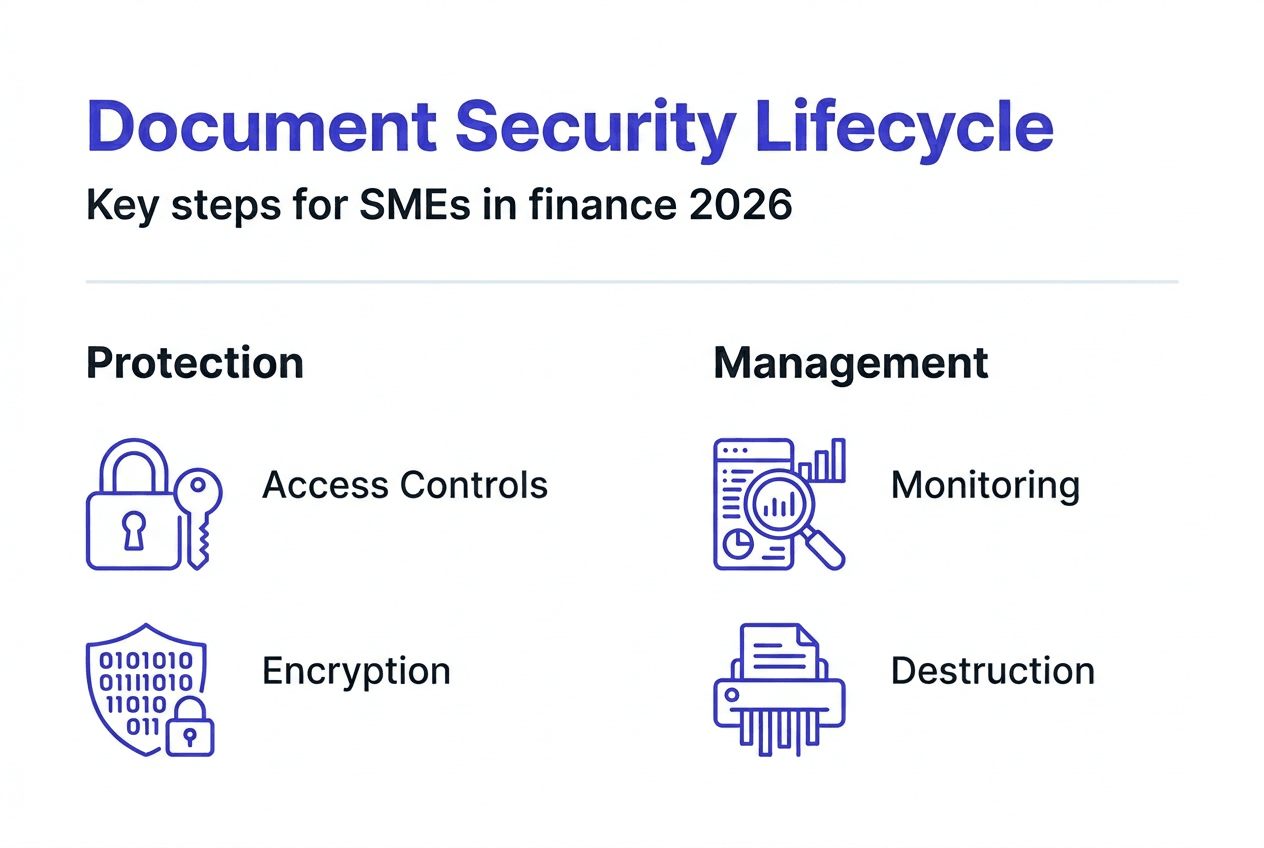
Document security frameworks provide structured approaches to protecting financial information from creation through disposal. These frameworks ensure sensitive data like bank statements, invoices, and transaction records remain confidential and accurate throughout their lifecycle.
A comprehensive framework includes several critical components. Data classification organizes information by sensitivity level, determining who can access what. Access controls limit document exposure to authorized personnel only. Encryption protects data both at rest and in transit, making intercepted information unreadable. Audit trails track every document interaction, creating accountability. Secure disposal methods ensure deleted data cannot be recovered by unauthorized parties.
Legal and regulatory requirements make these frameworks essential, not optional. Financial institutions and SMEs handling payment data must comply with PCI-DSS standards. Organizations processing personal financial information face GDPR obligations in many jurisdictions. Failure to implement proper security controls results in severe penalties and reputational damage.
Internal threats pose significant risks to financial document security. Studies show that insider threats account for nearly 60% of data breaches in accounting and finance departments. Employees with excessive access privileges, weak password practices, or malicious intent can compromise sensitive information. A robust framework addresses both external cyberattacks and internal vulnerabilities through role-based access and continuous monitoring.
Lifecycle management represents the backbone of effective document security. Financial documents require different protections at each stage. During creation, encryption and secure storage prevent unauthorized viewing. Active use demands strict access controls and version tracking. Archiving requires tamper-proof storage with retrieval capabilities. Final destruction must render data completely unrecoverable to prevent future breaches.
Pro Tip: Start your framework implementation by conducting a thorough data classification audit. Many SMEs discover they have been treating low-sensitivity documents with the same expensive controls as highly sensitive ones, wasting resources and creating unnecessary complexity.
Technologies and architectures securing financial documents in 2026
Zero trust architecture has revolutionized financial document security by abandoning the outdated perimeter defense model. This approach assumes no user or device is trustworthy by default, requiring continuous verification of identity and context before granting access. Organizations implementing zero trust principles see 60% fewer data breaches compared to traditional security models. Every access request undergoes real-time authentication, authorization, and encryption, creating multiple checkpoints that stop threats before they reach sensitive documents.
The proposed architecture combines zero trust principles with end-to-end encryption and robust identity management. Encryption standards like AES-256 protect financial data whether stored on servers or transmitted across networks. This military-grade encryption makes intercepted documents completely useless to attackers. PCI-DSS regulations mandate such encryption for any organization processing payment card information, making it a non-negotiable requirement for most SMEs.
Emerging technologies push security boundaries even further. Homomorphic encryption allows computation on encrypted data without decryption, enabling AI-powered analysis while maintaining privacy. Blockchain technology creates immutable audit trails for financial documents, preventing tampering and ensuring data integrity across distributed systems. These innovations provide SMEs with enterprise-level protection previously available only to large institutions.

AI-powered threat detection analyzes user behavior patterns to identify anomalies indicating potential breaches. Machine learning algorithms recognize suspicious access patterns, unusual download volumes, or unauthorized document modifications in real time. Automated key management systems rotate encryption keys regularly, reducing the window of vulnerability if a key becomes compromised. These technologies work together to create adaptive security that evolves with emerging threats.
Implementing advanced security technologies presents challenges for SMEs. Legacy financial systems often lack modern API capabilities, making integration complex and expensive. Encryption and real-time verification can introduce latency that slows document processing workflows. Key management complexity increases with each new security layer, requiring specialized expertise many small finance teams lack.
| Security Approach | Pros | Cons |
|---|---|---|
| Traditional perimeter defense | Lower initial cost, simpler implementation | Vulnerable to insider threats, outdated against modern attacks |
| Zero trust architecture | 60% breach reduction, continuous verification | Higher implementation complexity, potential latency |
| Cloud-based security | Scalable, automatic updates, lower maintenance | Dependency on provider, potential compliance concerns |
| Hybrid approach | Balances security and cost, gradual migration | Requires careful orchestration, temporary complexity |
Pro Tip: Start with cloud-based security for new document workflows while gradually migrating legacy systems. This hybrid approach lets you gain immediate protection without disrupting established processes, reducing both risk and implementation costs.
Navigating regulatory compliance and risk management with document security
Regulatory compliance drives document security requirements for SMEs in 2026. PCI-DSS mandates specific controls for organizations processing payment cards, including encryption and access restrictions. GDPR requires financial institutions to protect personal data with appropriate technical measures and document all processing activities. The Digital Operational Resilience Act introduces harmonized principles across EU financial entities, demanding comprehensive cyber resilience frameworks.
Document security directly minimizes compliance risks and the devastating penalties of non-compliance. Organizations failing to protect financial data face fines reaching 4% of annual revenue under GDPR. PCI-DSS violations result in increased processing fees, forensic audit costs, and potential loss of payment processing privileges. Beyond monetary penalties, breaches trigger mandatory disclosure requirements that damage customer trust and competitive position.
The financial impact of inadequate document security extends beyond regulatory fines. Data breaches cost organizations an average of $4.45 million in 2026, with financial services experiencing costs 28% above this baseline. These figures include incident response, legal fees, customer notification, credit monitoring services, and lost business. Recovery timelines average 287 days from detection to containment, during which normal operations suffer significant disruption.
Document security is not just a technical consideration but a legal and business imperative for regulated industries like finance. Organizations must implement comprehensive frameworks to avoid costly breaches, ensure compliance, and maintain operational resilience in an increasingly hostile threat landscape.
Operational resilience and business continuity depend on robust document security. Financial institutions must maintain access to critical records during and after security incidents. Automation enhances compliance capabilities by ensuring consistent application of security policies across all documents. Encrypted backups and geographically distributed storage prevent data loss from ransomware attacks or natural disasters.
Best practices for maintaining compliance evolve as regulations tighten and threats advance. SMEs should implement regular security audits to identify vulnerabilities before regulators do. Document all security policies, procedures, and incidents to demonstrate due diligence. Conduct staff training on data handling requirements and emerging phishing tactics. Engage legal counsel familiar with financial regulations to review frameworks annually. Enhance regulatory compliance through AI that automatically flags non-compliant document handling.
Risk management requires quantifying the probability and impact of document security failures. SMEs should conduct annual risk assessments that evaluate threat likelihood against potential financial and reputational damage. Prioritize security investments based on this analysis, focusing resources on highest-risk areas first. Document all risk decisions and mitigation strategies to satisfy regulatory expectations for governance.
Implementing document security best practices in SME finance operations
SMEs can implement effective document security through a systematic, phased approach that balances protection with operational efficiency. Follow these steps to build a robust framework tailored to your financial operations:
-
Conduct a comprehensive risk assessment identifying all financial documents, current security measures, and potential vulnerabilities. Map data flows from creation through disposal to spot exposure points.
-
Select a framework aligned with your compliance requirements and operational scale. NIST Cybersecurity Framework provides cost-effective guidance specifically designed for SME capabilities and budgets.
-
Implement data classification policies that categorize financial documents by sensitivity level. Apply appropriate controls to each category, avoiding over-protection of low-risk documents that wastes resources.
-
Deploy encryption for data at rest and in transit, starting with highest-sensitivity documents. Use AES-256 or equivalent standards that satisfy regulatory requirements.
-
Establish role-based access controls limiting document exposure to personnel requiring it for their duties. Review and update access privileges quarterly as responsibilities change.
-
Train all staff on document security policies, phishing recognition, and incident reporting procedures. Make security awareness ongoing, not a one-time orientation.
-
Implement automated monitoring and alerting for suspicious document access patterns or policy violations. User behavior analytics frameworks make this practical and affordable for SMEs.
-
Conduct regular security audits testing control effectiveness and identifying emerging vulnerabilities. Schedule penetration testing annually to validate defenses against real-world attack techniques.
-
Develop and test incident response plans detailing specific actions when breaches occur. Designate response team members and establish communication protocols before emergencies arise.
-
Automate financial document processing to reduce human error and enforce consistent security policies across all transactions.
Multilayered security provides the most cost-effective protection by creating redundant defenses that compensate for individual control failures. Combine network security, endpoint protection, access controls, encryption, and monitoring. Attackers must breach multiple independent systems to access financial documents, exponentially increasing their effort while your costs scale linearly.
Automation and AI improve both security and accuracy in financial record management. Machine learning algorithms detect anomalies humans miss in vast transaction volumes. Automated workflows enforce security policies without relying on employee compliance. AI-powered processing achieves 99% accuracy while maintaining strict access controls and audit trails.
Continuous adaptation keeps security effective as threats evolve. Cyber criminals constantly develop new attack vectors targeting financial data. Subscribe to threat intelligence feeds relevant to your industry. Update security controls quarterly based on emerging attack patterns. Participate in information sharing groups where SMEs exchange threat data and mitigation strategies.
Pro Tip: Review your data classification and access policies every six months rather than annually. Employee roles change frequently in SMEs, and outdated access privileges create the most common security vulnerabilities. A quick quarterly review takes minimal time but prevents the majority of insider threat incidents.
Explore AI-powered document security solutions
Transforming financial document management requires more than understanding security principles. You need practical tools that deliver both protection and efficiency. BankStatementFlow combines AI-powered automation with enterprise-grade security to process bank statements, invoices, and receipts while maintaining strict data protection.
The platform encrypts all documents during processing and stores nothing after conversion completes, eliminating long-term breach risks. Access controls limit document exposure to authorized users only. Comprehensive audit trails track every interaction for compliance verification. Processing accuracy reaches 99%, reducing the errors that create security vulnerabilities in manual workflows. Explore how AI-driven automation secures your financial document operations while improving speed and accuracy.
FAQ
What is the role of document security in finance?
Document security protects sensitive financial data from unauthorized access, modification, or destruction throughout its lifecycle. It ensures accuracy, maintains compliance with regulations like PCI-DSS and GDPR, and prevents costly breaches that average $5.9 million per incident in 2026.
How does zero trust architecture improve financial document security?
Zero trust architecture continuously verifies user identity and device health before granting document access, eliminating implicit trust. Organizations adopting zero trust principles reduce breaches by 60% by requiring authentication for every access request rather than relying on perimeter defenses.
What compliance regulations impact document security in SME finance?
PCI-DSS mandates encryption and access controls for payment card data. GDPR requires appropriate technical measures protecting personal financial information. DORA introduces operational resilience requirements across EU financial entities. Compliance automation helps SMEs meet these evolving standards efficiently.
How can SMEs adopt cost-effective document security practices?
Implement multilayered security aligned with NIST Cybersecurity Framework, focusing resources on highest-risk areas first. Use automated user behavior analytics to detect threats cost-effectively. Automate document processing workflows to enforce consistent security policies while reducing manual errors and operational costs.
Recommended
- Financial document checklist for SMEs: boost accuracy - BankStatementFlow Blog
- Trends in Financial Automation 2026: What CFOs Need - BankStatementFlow Blog
- Data Security in Financial Document Processing: What You Need to Know - BankStatementFlow Blog
- Document Automation Examples: 99% Accuracy for Accounting - BankStatementFlow Blog